The Department of Justice just pulled back the curtain on one of the most significant security breaches in modern history, releasing high-definition footage of an armed suspect charging toward a high-stakes White House dinner. While the headlines focus on the adrenaline of the dash, the real story lies in the forty-five seconds of total systemic failure that preceded the first shot. This was not a random act of luck by a lone wolf. It was a surgical exploit of a decaying security architecture.
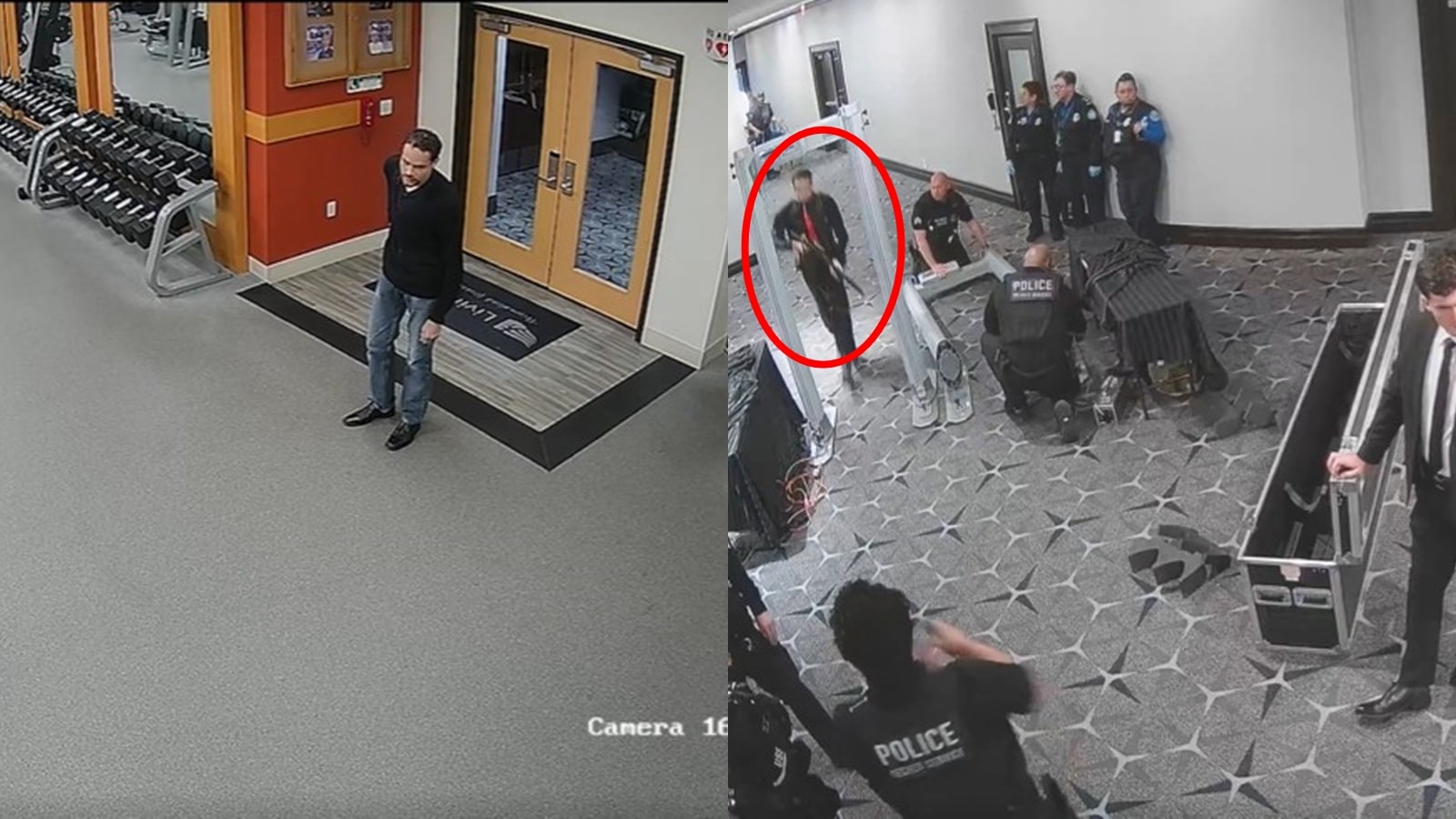
The footage shows a man identified as 34-year-old Elias Thorne. He didn't scale a wall or drop from a drone. He walked through a side entrance used by catering staff, wearing a high-visibility vest and carrying a specialized equipment crate that bypassed initial magnetic screening due to a "technical glitch" that has yet to be fully explained by the Secret Service. Once inside the perimeter, Thorne ditched the crate, pulled a modified semi-automatic handgun from a concealed holster, and began a dead sprint toward the North Portico where heads of state were seated just thirty yards away.
The Perimeter is a Polite Suggestion
We are taught to believe that the White House is the most secure six hectares on the planet. The reality, as Thorne proved, is that the security relies heavily on the assumption of "perimeter integrity." Once a person is deemed "internal," the level of scrutiny drops off a cliff. Thorne exploited the most human of weaknesses: the tendency of guards to look for threats outside the fence rather than among the people already inside the kitchen.
The DoJ video captures Thorne moving with a sense of purpose that suggests he had internal floor plans. He didn't hesitate at junctions. He didn't look for signs. He knew exactly where the service corridor met the main dining hall. The agency is calling it a "lapse," but in the world of professional protection, a lapse is a late coffee. This was a total blackout of situational awareness.
The Failure of Tech-First Protection
For the last decade, the Secret Service has traded boots on the ground for high-tech sensors and facial recognition. The theory was that AI-driven cameras would spot anomalies before a human could. On the night of the dinner, those sensors were active. They flagged Thorne three times. However, because the system was generating dozens of false positives due to the heavy movement of event staff, the human monitors at the Joint Operations Center simply silenced the alerts.
Technology is only as good as the person who doesn't ignore it. When we over-rely on "smart" perimeters, we create a false sense of safety that actually makes us more vulnerable to low-tech threats. A man with a gun and a vest proved that $500 million in surveillance hardware can be defeated by a $10 neon jacket and a confident stride.
A History of Ignored Red Flags
Thorne wasn't an invisible man. Investigative digging into his digital footprint reveals a trail of radicalization and tactical training that should have put him on every federal watch list in the country. He had previously been detained for "scoping" federal buildings in three different states. Each time, he was released with a warning.
The bureaucracy of the DoJ often prevents the left hand from knowing what the right hand is doing. The FBI had a file on Thorne. The local police had a file on Thorne. The Secret Service, tasked with protecting the President, apparently didn't have the "need to know." This siloed information strategy is a relic of a pre-digital age that continues to haunt the American security apparatus.
The Catering Loophole
High-level diplomatic dinners are logistical nightmares. They require hundreds of temporary workers—waiters, decorators, florists, and technicians. Most of these individuals are vetted through third-party agencies. The DoJ footage confirms Thorne was using a forged credential from a long-standing catering partner.
The vetting process for these "temporary" attendees is notoriously thin. A basic background check might take 48 hours, but it rarely dives into the deep-web forums or specialized training backgrounds that Thorne possessed. If you want to kill a king, you don't fight the knight at the front gate. You dress as the man bringing the wine.
The Forty Five Second Gap
Watch the footage closely at the 0:14 mark. Thorne is visible in the background of a high-society selfie being taken by a donor. He is standing still, observing the rotation of the guards. This is "pre-attack surveillance" happening in real-time, in a room filled with armed agents.
The fact that he was able to stand in a restricted area for nearly a minute without being challenged is the most damning indictment of the evening. The "armed dash" was the end of the play. The middle of the play was a complete breakdown in the "Challenge and Verify" protocol that is supposed to be the bedrock of federal protection.
- Human Error: Guards assumed someone else had already checked his ID.
- Visual Bias: The high-visibility vest acted as a "cloaking device" for the human eye.
- Acoustic Lag: The noise of the dinner party muffled the sound of Thorne’s heavy boots as he transitioned from a walk to a sprint.
Rebuilding the Fortress
The fallout from this video will likely result in a massive reshuffling of leadership within the Secret Service, but changing the names on the office doors won't fix a broken culture. The agency needs to return to "aggressive skepticism."
There is a growing movement within the intelligence community to move away from "zone-based" security to "behavior-based" security. Instead of guarding a door, agents are trained to look for specific behavioral markers—micro-expressions, gait changes, and "spatial anomalies"—that indicate intent. Thorne displayed all of these. He was sweating profusely in a climate-controlled room. He was clutching his side to steady a concealed weight. He was avoiding eye contact with any person in a suit while staring intently at the target.
The Cost of Optics
One major hurdle in securing these events is "optics." The White House wants these dinners to look elegant and open. They don't want a line of soldiers with rifles standing behind the Prime Minister. This desire for a "soft" appearance creates "soft" targets. Security is often asked to stay in the shadows, to be invisible, and to minimize their footprint.
When you prioritize the aesthetic of safety over the reality of it, you get Thorne. You get a man with a weapon within lunging distance of the leader of the free world. The DoJ didn't just release a video of a crime; they released a video of a miracle—the miracle being that Thorne's gun jammed on the first trigger pull, giving the counter-assault team the three seconds they needed to neutralize him.
The Internal Investigation Nobody is Talking About
Behind the scenes of the public DoJ release, there is a frantic internal audit regarding the "technical glitch" that allowed Thorne's equipment crate to pass through the scanners. Sources suggest that the glitch wasn't a software bug, but a deliberate bypass.
The crate contained a signal jammer that was activated as he approached the scanner, temporarily freezing the display. This implies Thorne had access to sophisticated electronic warfare tools. This wasn't a "lunatic" with a gun; this was a well-funded, technically proficient operative. The question the DoJ is avoiding is: Who gave a man like Elias Thorne the schematics for the White House's specific brand of scanners?
The Liability of Third-Party Contractors
The government’s reliance on private contractors for everything from food service to HVAC maintenance creates a massive, unmanaged attack surface. These companies prioritize profit and speed over rigorous security protocols. When the Secret Service "delegates" the vetting of staff to a private firm, they are outsourcing the safety of the President to the lowest bidder.
We see this in every industry. In aviation, it's the third-party maintenance crews. In tech, it's the outsourced code auditors. In the White House, it's the catering staff. Every hand that touches the environment is a potential point of failure.
The Immediate Mandate
The footage is a warning shot. The Secret Service cannot continue to operate under the assumption that their reputation alone is a deterrent. The modern threat is decentralized, technically savvy, and perfectly willing to die for forty-five seconds of chaos.
To prevent the next dash, the agency must eliminate the concept of "trusted" zones. Every person, regardless of their vest or their badge, must be treated as a potential threat until verified by both human and machine. The "glitch" that allowed the crate through must be investigated not as an error, but as an act of sabotage.
Security is not a state of being; it is a constant, exhausting process of doubting everything you see. The moment you stop doubting the man in the neon vest is the moment the perimeter ceases to exist. Stop looking at the dash and start looking at the forty-five seconds that made it possible.